The Panic mode privacy option allows protecting a cloned app’s internal data in case of phone theft, tactical ‘snatching’ by law enforcement or other unauthorized access of your device.
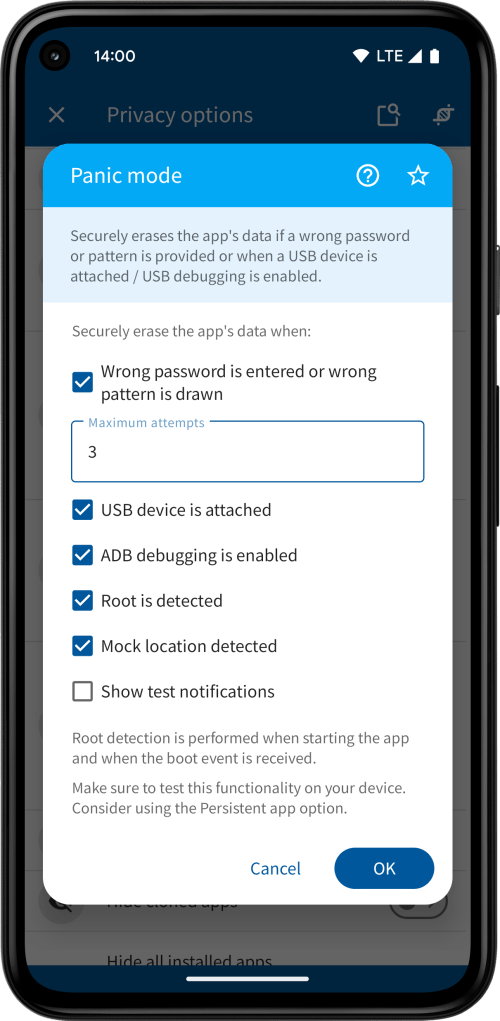
Specifically, the option will securely erase the internal app data and files when:
- A wrong password is entered or a wrong pattern is drawn (this option is available for apps that are password or pattern-protected and you may specify the maximum number of attempts)
- A USB device is attached (e.g. a forensic tool that facilitates data recovery)
- ADB debugging is enabled (ADB debugging allows installing foreign applications and retrieving files from your phone)
- Root is detected (a rooted phone allows full access to internal files of all apps)
- Mock location is detected
Root detection is performed when starting the app or when the boot event is received, whichever comes first. Rooting a phone always requires the device to be rebooted. The root detection method uses a variety of indicators.
Mock location detection is performed periodically while the app is running. Detecting mock locations requires the location permission to be granted. If it’s not granted the cloned app will show the permission prompt and exit.
Secure erasing of files is done by overwriting the file contents, replacing the file name and extension with dummy characters followed by permanently deleting the file. Note that depending on the size of the internal files this process may take some time.
Since this functionality depends on certain system events being triggered in a timely manner, it’s highly recommended for you to test the behavior on your device by enabling the Show test notifications checkbox. This shows a notification when the panic mode is activated and the app data is erased. While testing, make sure App Cloner is running.
It’s also recommended to use the Persistent app option and create a dummy accessibility service, which ensures the app is always kept alive and won’t be put to sleep by the system, in which case the app may not receive any events.

You must be logged in to post a comment.